cisco 300-215 practice test
conducting forensic analysis and incident response using cisco cyberops technologies (cbrfir)
Last exam update: Apr 14 ,2025
Question 1
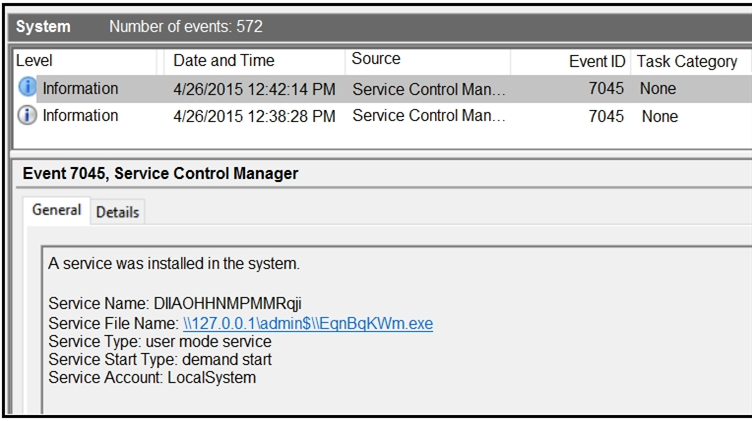
Refer to the exhibit. An HR department submitted a ticket to the IT helpdesk indicating slow performance on an internal share server. The helpdesk engineer checked the server with a real-time monitoring tool and did not notice anything suspicious. After checking the event logs, the engineer noticed an event that occurred 48 hour prior. Which two indicators of compromise should be determined from this information? (Choose two.)
- A. unauthorized system modification
- B. privilege escalation
- C. denial of service attack
- D. compromised root access
- E. malware outbreak
Answer:
ad
Question 2
An employee receives an email from a trusted person containing a hyperlink that is malvertising. The employee clicks the link and the malware downloads. An information analyst observes an alert at the SIEM and engages the cybersecurity team to conduct an analysis of this incident in accordance with the incident response plan. Which event detail should be included in this root cause analysis?
- A. phishing email sent to the victim
- B. alarm raised by the SIEM
- C. information from the email header
- D. alert identified by the cybersecurity team
Answer:
b
Question 3
A security team detected an above-average amount of inbound tcp/135 connection attempts from unidentified senders. The security team is responding based on their incident response playbook. Which two elements are part of the eradication phase for this incident? (Choose two.)
- A. anti-malware software
- B. data and workload isolation
- C. centralized user management
- D. intrusion prevention system
- E. enterprise block listing solution
Answer:
cd
Question 4
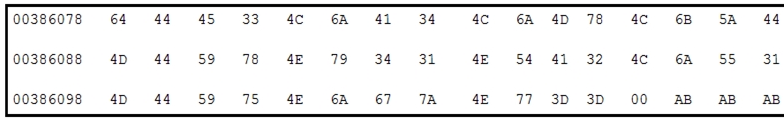
Refer to the exhibit. Which encoding technique is represented by this HEX string?
- A. Unicode
- B. Binary
- C. Base64
- D. Charcode
Answer:
b
Reference:
https://www.suse.com/c/making-sense-hexdump/
Question 5
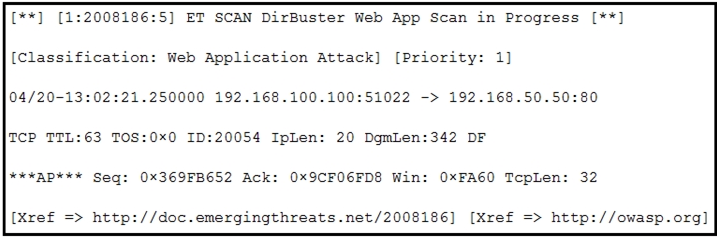
Refer to the exhibit. According to the SNORT alert, what is the attacker performing?
- A. brute-force attack against the web application user accounts
- B. XSS attack against the target webserver
- C. brute-force attack against directories and files on the target webserver
- D. SQL injection attack against the target webserver
Answer:
c
Question 6
What is the transmogrify anti-forensics technique?
- A. hiding a section of a malicious file in unused areas of a file
- B. sending malicious files over a public network by encapsulation
- C. concealing malicious files in ordinary or unsuspecting places
- D. changing the file header of a malicious file to another file type
Answer:
d
Reference:
https://www.csoonline.com/article/2122329/the-rise-of-anti-forensics.html#:~:text=Transmogrify%20is%20similarly%20wise%20to,a%20file%20from%2C%20say%
2C%20
.
Question 7
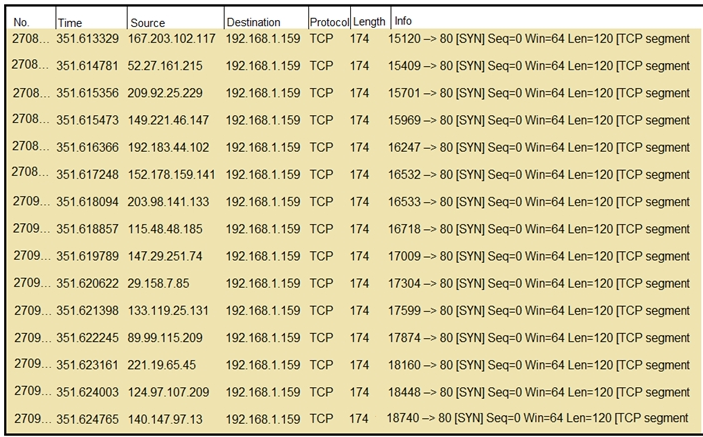
Refer to the exhibit. What should an engineer determine from this Wireshark capture of suspicious network traffic?
- A. There are signs of SYN flood attack, and the engineer should increase the backlog and recycle the oldest half-open TCP connections.
- B. There are signs of a malformed packet attack, and the engineer should limit the packet size and set a threshold of bytes as a countermeasure.
- C. There are signs of a DNS attack, and the engineer should hide the BIND version and restrict zone transfers as a countermeasure.
- D. There are signs of ARP spoofing, and the engineer should use Static ARP entries and IP address-to-MAC address mappings as a countermeasure.
Answer:
a
Question 8
An engineer is investigating a ticket from the accounting department in which a user discovered an unexpected application on their workstation. Several alerts are seen from the intrusion detection system of unknown outgoing internet traffic from this workstation. The engineer also notices a degraded processing capability, which complicates the analysis process. Which two actions should the engineer take? (Choose two.)
- A. Restore to a system recovery point.
- B. Replace the faulty CPU.
- C. Disconnect from the network.
- D. Format the workstation drives.
- E. Take an image of the workstation.
Answer:
ae
Question 9
A security team is discussing lessons learned and suggesting process changes after a security breach incident. During the incident, members of the security team failed to report the abnormal system activity due to a high project workload. Additionally, when the incident was identified, the response took six hours due to management being unavailable to provide the approvals needed. Which two steps will prevent these issues from occurring in the future? (Choose two.)
- A. Introduce a priority rating for incident response workloads.
- B. Provide phishing awareness training for the fill security team.
- C. Conduct a risk audit of the incident response workflow.
- D. Create an executive team delegation plan.
- E. Automate security alert timeframes with escalation triggers.
Answer:
ae
Question 10
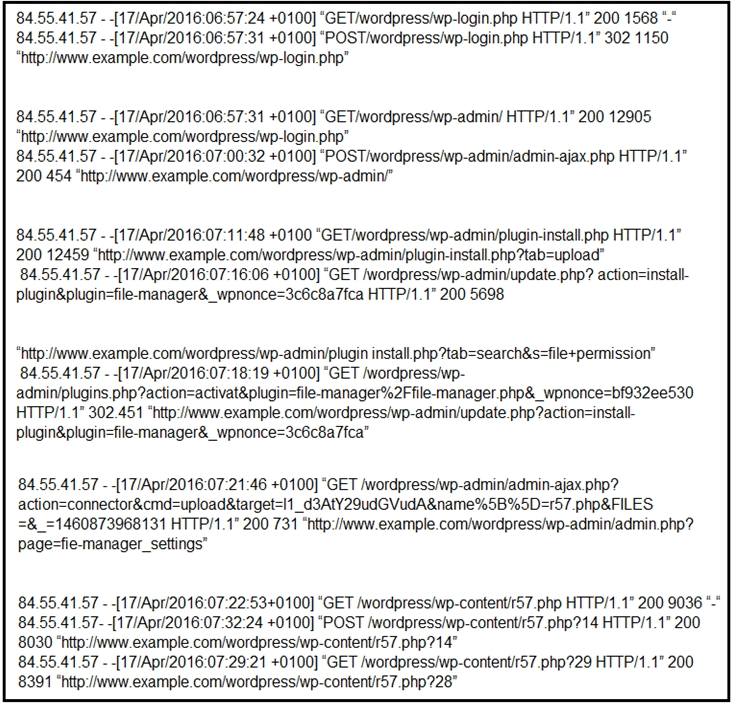
Refer to the exhibit. Which two determinations should be made about the attack from the Apache access logs? (Choose two.)
- A. The attacker used r57 exploit to elevate their privilege.
- B. The attacker uploaded the word press file manager trojan.
- C. The attacker performed a brute force attack against word press and used sql injection against the backend database.
- D. The attacker used the word press file manager plugin to upoad r57.php.
- E. The attacker logged on normally to word press admin page.
Answer:
cd